On This Page
Introduction
After the deployment of software, there is usually an ongoing need for feature enhancement, new features, or adapting to external changes requiring updates. Whether the software was originally developed by Project Balance, another vendor, or your in-house team, we apply the same best practices to the new development in this maintenance phase as we would for any other project.
We collaborate with you to define your needs and build a prioritized list of enhancements and updates. Leveraging Agile principles, you and your team choose the highest-value items, which we tackle first. These enhancements can be addressed through focused mini-projects or via ongoing support from a dedicated small team. We’ll also work with you to optimize your budget for maintenance, ensuring the long-term viability of your digital assets.
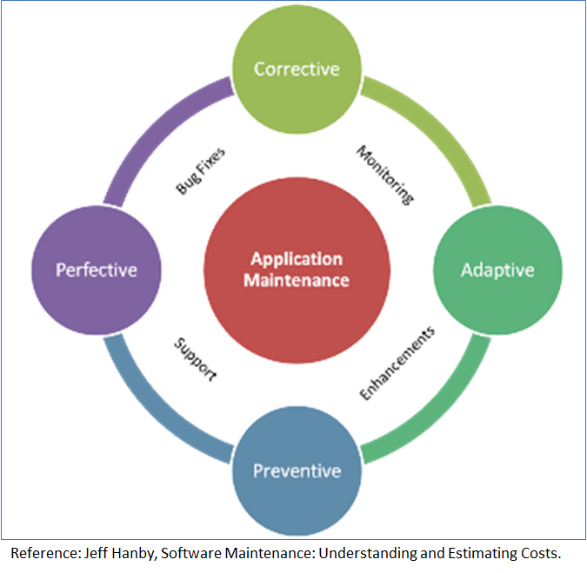
Project Balance covers all four different types of maintenance activities including:
- Corrective – fixing defects
- Adaptive – handling impacts to an application as a result of a component outside of the software changing, such as a change in a third-party feature or possibly an operating system change.
- Preventive – Update the software to detect and correct potential faults in the software product before they take effect such as optimizing queries as the size of the database grows or monitoring your server for outages.
- Perfective – Usually as a result of user feedback, enhancing existing and adding new features and functions of the software.
Hosting and Server Monitoring
When Project Balance develops software, we begin by configuring a QA server and then mirror those optimized settings on a production server. Your production server can be hosted either by us or within your own environment. Our hosting services encompass uptime monitoring, scheduled database backups, and disaster recovery planning. We utilize tools like Sentry.io for error tracking and Greenbone Vulnerability Monitor for security alerts.
Cybersecurity
Recognizing the dramatic rise in cyber threats over the last two decades, Project Balance understands that these threats will likely continue to evolve alongside the increasing reliance on digital-first, always-on business models, high-speed connectivity, and the expansion of remote workforces. Given our deep understanding of breach vulnerabilities, we prioritize security, implementing robust measures to protect both our own and our clients’ systems. These measures include comprehensive staff training and dedicated development environments for each project. We strongly recommend modern, secure remote access technologies such as Zero Trust Network Access (ZTNA), Virtual Desktop Infrastructure (VDI), Virtual Private Networks (VPNs), and leveraging your existing SD-WAN environment where applicable to securely connect to your production network and mitigate risks.